Managed IT support is an essential resource for businesses navigating today’s digital landscape. Whether you’re a small business in Auckland or a growing enterprise across New Zealand, recognising the signs that you need professional IT support can save you time, money and stress. Benefits of Managed IT Support Reduced Downtime: Proactive monitoring and maintenance preventRead more
Blog
The rapid advancement of technology has made Managed IT support an indispensable aspect of business operations. In Auckland, the demand for efficient and reliable IT support services continues to grow, spotlighting the need for managed service providers (MSPs). This article aims to provide a comprehensive guide to understanding managed IT services, exploring the key offeringsRead more
Microsoft 365 is an indispensable tool for businesses of all sizes and for this reason, it has become vital to implement Microsoft 365 backups. With its suite of applications like Word, Excel, Outlook, and OneDrive, it streamlines operations and fosters collaboration. However, many users mistakenly believe that their data is completely safe just because it’sRead more
In the rapidly evolving digital landscape, companies face an ever-growing challenge to protect their company data and maintain operational continuity. As the first line of defence against cyber breaches, firewalls play a pivotal role in safeguarding company data by forming a barrier between the external world and their network. In this blog post, we delveRead more
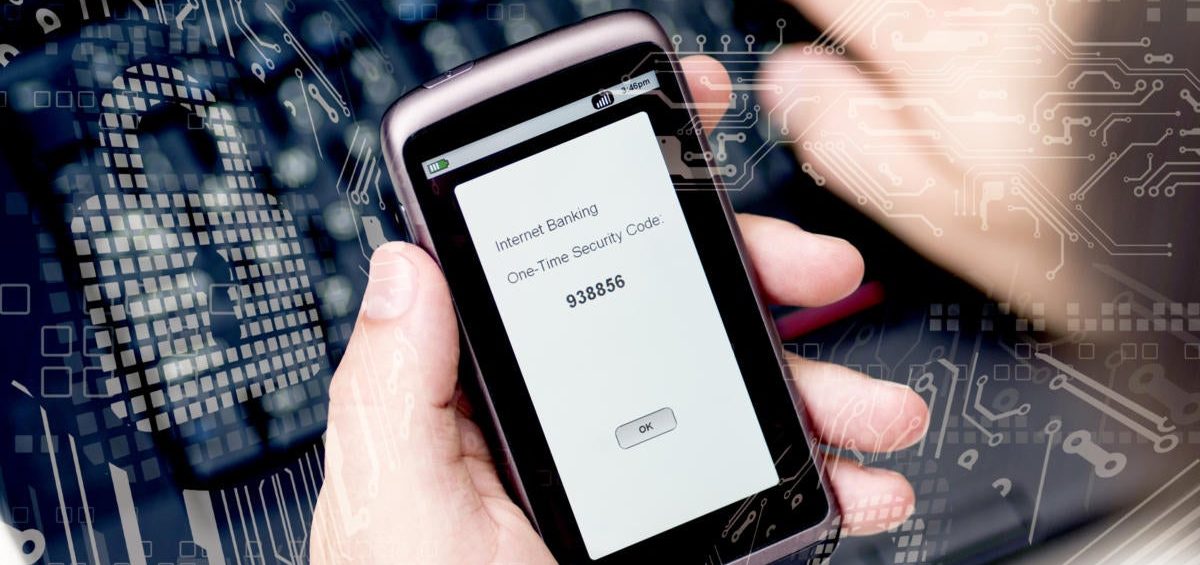
In today’s digital landscape, where cyber threats are rampant, protecting our online accounts has become more crucial than ever. One of the most effective ways to fortify our digital presence is through multifactor authentication (MFA). This powerful security measure adds an extra layer of protection, making it significantly harder for unauthorised individuals to access ourRead more
Technical difficulties whilst working from home, can leave you feeling frustrated. Here are a few basic best practice and troubleshooting tips so that you can power through your day. Practice cyber security awareness Some security measures that are in place at your workplace, may not be in place on your home network. These include securityRead more
It’s easy to add an extra layer of security to your accounts and devices by adding on two-step verification — also known as multi-factor, two-factor or two-step authentication. Why you need it Passwords can be guessed or stolen. With two-factor authentication, even if an attacker gets your password, it won’t be enough to sign intoRead more
Emails are often our main form of communication with our clients, prospects and colleagues. Each email is not just an opportunity to send a message, it also offers a space for building your brand, advertising and engaging with your recipient. Email Signatures are the perfect tool to deliver all of the above. They also offerRead more
In a security context, human error means unintentional actions – or lack of action – by employees and users that cause, spread or allow a security breach to take place. Almost all successful cyber breaches share one thing in common: human error. According to a study by IBM, human error is the main cause ofRead more
Imagine going back to the office after a long holiday, only to be greeted by a messy workstation. If your company wants clean, organised technology, this IT hardware checklist is just what you need. ✓ Clean up your computer components Wipe your monitor with clean, static-free fabric; remove excess dirt from your mouse’s exterior; and tidyRead more